Java Deserialization Vulnerabilities - The Forgotten Bug Class
- 1. Java Deserialization Vulnerabilities – The Forgotten Bug Class Matthias Kaiser (@matthias_kaiser)
- 2. About me Head of Vulnerability Research at Code White in Ulm, Germany Specialized on (server-side) Java Found bugs in products of Oracle, VMware, IBM, SAP, Symantec, Apache, Adobe, etc. Recently looking more into the Windows world and client-side stuff 4/7/2016 @matthias_kaiser
- 3. Agenda Introduction Java’s Object Serialization What’s the problem with it A history of bugs Finding and exploiting Code White’s bug parade + a gift for Infiltrate More to come? 4/7/2016
- 4. Should you care? If your client is running server products of 4/7/2016 you SHOULD!
- 5. Some facts The bug class exists for more than 10 years Most ignored bug class in the server-side Java world until 2015 A easy way to get reliable RCE on a server Architecture independent exploitation With Java deserialization vulnerabilities you can pwn a corp easily! 4/7/2016
- 6. Where is it used Several J2EE/JEE core technologies rely on serialization Remote Method Invocation (RMI) Java Management Extension (JMX) Java Message Service (JMS) Java Server Faces implementations (ViewState) Communication between JVMs in general (because devs are lazy :-) Custom application protocols running on top of http, etc. 4/7/2016
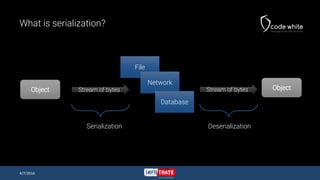
- 7. What is serialization? 4/7/2016 Object File Network Database ObjectStream of bytes Stream of bytes Serialization Deserialization
- 8. Overview of Java’s Object Serialization Protocol 4/7/2016 Magic class name field type class field Class description info TC_OBJECT TC_CLASSDESC classdata[]
- 9. There is protocol spec and a grammar 4/7/2016 https://docs.oracle.com/javase/8/docs/platform/serialization/spec/protocol.html
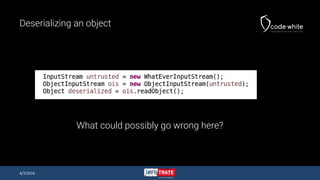
- 10. Deserializing an object What could possibly go wrong here? 4/7/2016
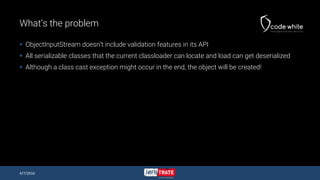
- 11. What’s the problem ObjectInputStream doesn’t include validation features in its API All serializable classes that the current classloader can locate and load can get deserialized Although a class cast exception might occur in the end, the object will be created! 4/7/2016
- 12. What’s the problem #2 A developer can customize the (de)-serialization of a serializable class Implement methods writeObject(), writeReplace(), readObject() and readResolve() ObjectInputStream invokes readObject() and readResolve() 4/7/2016 Under our control!
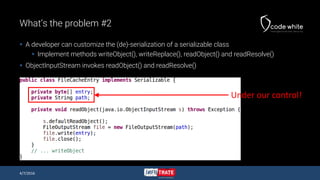
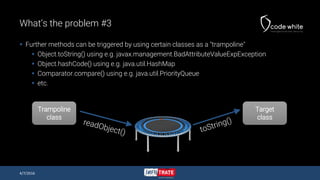
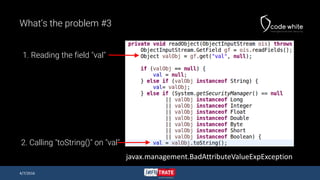
- 13. What’s the problem #3 Further methods can be triggered by using certain classes as a "trampoline" Object.toString() using e.g. javax.management.BadAttributeValueExpException Object.hashCode() using e.g. java.util.HashMap Comparator.compare() using e.g. java.util.PriorityQueue etc. 4/7/2016 Trampoline class Target class
- 14. What’s the problem #3 4/7/2016 javax.management.BadAttributeValueExpException 1. Reading the field "val" 2. Calling "toString()" on "val"
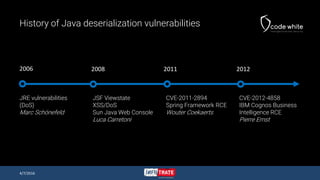
- 15. History of Java deserialization vulnerabilities JRE vulnerabilities (DoS) Marc Schönefeld 2006 JSF Viewstate XSS/DoS Sun Java Web Console Luca Carretoni 2008 CVE-2011-2894 Spring Framework RCE Wouter Coekaerts CVE-2012-4858 IBM Cognos Business Intelligence RCE Pierre Ernst 2011 2012 4/7/2016
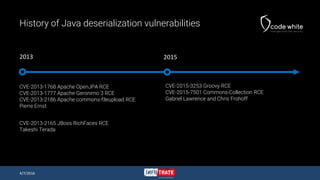
- 16. History of Java deserialization vulnerabilities CVE-2013-1768 Apache OpenJPA RCE CVE-2013-1777 Apache Geronimo 3 RCE CVE-2013-2186 Apache commons-fileupload RCE Pierre Ernst CVE-2015-3253 Groovy RCE CVE-2015-7501 Commons-Collection RCE Gabriel Lawrence and Chris Frohoff CVE-2013-2165 JBoss RichFaces RCE Takeshi Terada 2013 2015 4/7/2016
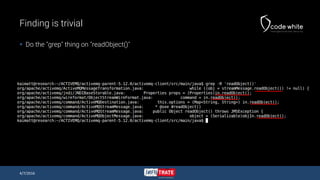
- 17. Finding is trivial Do the "grep" thing on "readObject()" 4/7/2016
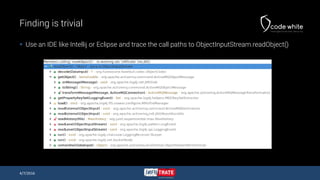
- 18. Finding is trivial Use an IDE like Intellij or Eclipse and trace the call paths to ObjectInputStream.readObject() 4/7/2016
- 19. Exploitation Exploitation requires a chain of serialized objects triggering interesting functionality e.g. writing files dynamic method calls using Java’s Reflection API etc. For such a chain the term "gadget" got established Chris Frohoff and others found several gadgets in standard libs Let’s look at an example gadget 4/7/2016
- 20. Javassist/Weld Gadget Gadget utilizes JBoss’ Javassist and Weld framework Reported to Oracle with the Weblogic T3 vulnerability Works in Oracle Weblogic and JBoss EAP Allows us to call a method on a deserialized object 4/7/2016
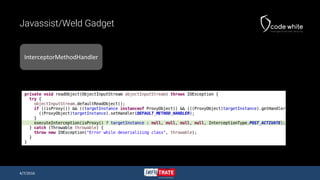
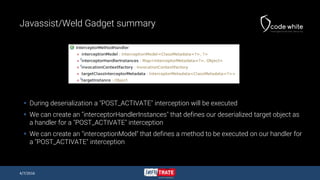
- 22. Javassist/Weld Gadget summary During deserialization a "POST_ACTIVATE" interception will be executed We can create an "interceptorHandlerInstances" that defines our deserialized target object as a handler for a "POST_ACTIVATE" interception We can create an "interceptionModel" that defines a method to be executed on our handler for a "POST_ACTIVATE" interception 4/7/2016
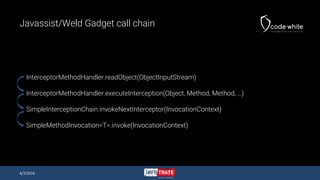
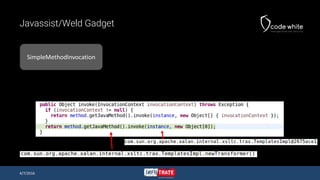
- 23. Javassist/Weld Gadget call chain InterceptorMethodHandler.readObject(ObjectInputStream) InterceptorMethodHandler.executeInterception(Object, Method, Method, …) SimpleInterceptionChain.invokeNextInterceptor(InvocationContext) SimpleMethodInvocation<T>.invoke(InvocationContext) 4/7/2016
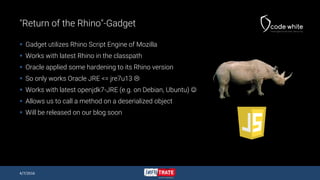
- 25. "Return of the Rhino"-Gadget Gadget utilizes Rhino Script Engine of Mozilla Works with latest Rhino in the classpath Oracle applied some hardening to its Rhino version So only works Oracle JRE <= jre7u13 Works with latest openjdk7-JRE (e.g. on Debian, Ubuntu) Allows us to call a method on a deserialized object Will be released on our blog soon 4/7/2016
- 26. What to look for? Look for methods in serializable classes working on files triggering reflection (invoking methods, getting/setting properties on beans) doing native calls etc. AND being called from readObject() readResolve() toString() hashCode() finalize() any other method being called from a "Trampoline" class 4/7/2016
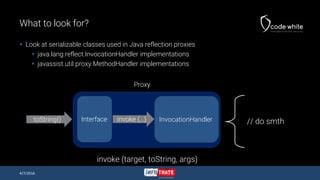
- 27. What to look for? Look at serializable classes used in Java reflection proxies java.lang.reflect.InvocationHandler implementations javassist.util.proxy.MethodHandler implementations 4/7/2016 InvocationHandlerInterface Proxy toString() invoke (…) // do smth invoke (target, toString, args)
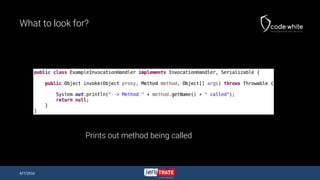
- 28. What to look for? 4/7/2016 Prints out method being called
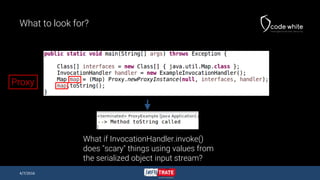
- 29. What to look for? 4/7/2016 What if InvocationHandler.invoke() does "scary" things using values from the serialized object input stream? Proxy
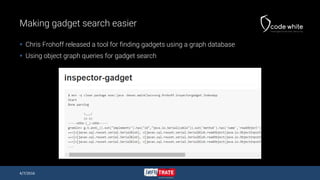
- 30. Making gadget search easier Chris Frohoff released a tool for finding gadgets using a graph database Using object graph queries for gadget search 4/7/2016
- 31. Exploitation tricks Adam Gowdiak’s TemplatesImpl com.sun.org.apache.xalan.internal.xsltc.trax.TemplatesImpl is serializable Allows to define new classes from your byte[ ][ ] Calling TemplatesImpl.newTransformer() on deserialized object Code Execution 4/7/2016
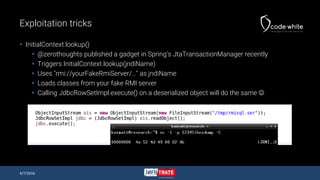
- 32. Exploitation tricks InitialContext.lookup() @zerothoughts published a gadget in Spring’s JtaTransactionManager recently Triggers InitialContext.lookup(jndiName) Uses "rmi://yourFakeRmiServer/…" as jndiName Loads classes from your fake RMI server Calling JdbcRowSetImpl.execute() on a deserialized object will do the same 4/7/2016
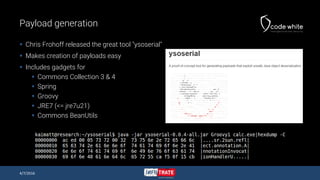
- 33. Payload generation Chris Frohoff released the great tool "ysoserial" Makes creation of payloads easy Includes gadgets for Commons Collection 3 & 4 Spring Groovy JRE7 (<= jre7u21) Commons BeanUtils 4/7/2016
- 34. Custom payloads I wouldn’t go for Runtime.getRuntime().exec(cmd) for several reasons Most of the gadgets don’t touch the disk With scripting languages your life gets even easier Use what’s in the classpath Javascript (Rhino, Nashorn) Groovy Beanshell etc. 4/7/2016
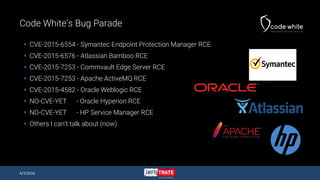
- 35. Code White’s Bug Parade CVE-2015-6554 - Symantec Endpoint Protection Manager RCE CVE-2015-6576 - Atlassian Bamboo RCE CVE-2015-7253 - Commvault Edge Server RCE CVE-2015-7253 - Apache ActiveMQ RCE CVE-2015-4582 - Oracle Weblogic RCE NO-CVE-YET - Oracle Hyperion RCE NO-CVE-YET - HP Service Manager RCE Others I can’t talk about (now) 4/7/2016
- 37. Oracle Weblogic Oracle’s Application Server (acquired from BEA) Middleware for core products of Oracle Oracle Enterprise Manager Oracle VM Manager Oracle ESB Oracle Hyperion Oracle Peoplesoft And many more 4/7/2016
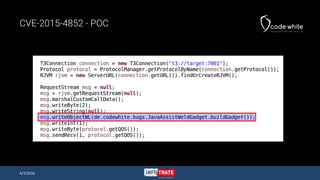
- 38. CVE-2015-4852 - Oracle Weblogic Reported on 21st of July 2015 to Oracle as "Oracle Weblogic T3 Deserialization Remote Code Execution Vulnerability" Detailed advisory with POCs Using Chris Frohoff’s Commons Collection Gadget Using my Javassist/Weld Gadget I recommended to implement "Look-ahead Deserialization" by Pierre Ernst Yeah, the one @foxglovesec dropped … 4/7/2016
- 39. CVE-2015-4852 - Oracle Weblogic Weblogic uses multi-protocol listener architecture Channels can be defined listening for several protocols The "interesting" protocols are t3 and t3s 4/7/2016
- 40. CVE-2015-4852 - T3 Protocol Weblogic has its own RMI protocol called T3 Exists since the early days of Weblogic Used for JEE remoting (e.g. Session Beans) Used for JMX (e.g. by Weblogic Scripting Tool) Can also be tunneled over HTTP (if enabled) Check http://target:port/bea_wls_internal/HTTPClntLogin/a.tun 4/7/2016
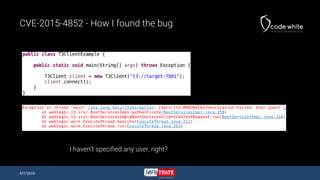
- 41. CVE-2015-4852 - How I found the bug Found during my daughter’s midday nap ;-) Remembered the time when I was Dev and writing software for NATO systems We used to deploy software on Weblogic using T3 Just wrote some lines to create a T3 connection 4/7/2016
- 42. CVE-2015-4852 - How I found the bug 4/7/2016 I haven’t specified any user, right?
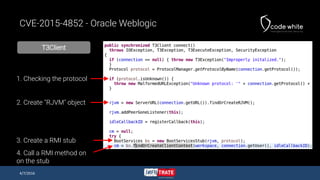
- 43. T3Client CVE-2015-4852 - Oracle Weblogic 4/7/2016 1. Checking the protocol 2. Create "RJVM" object 4. Call a RMI method on on the stub 3. Create a RMI stub
- 44. BootServicesStub CVE-2015-4852 - Oracle Weblogic 4/7/2016 Method id 2 Serializing a UserInfo object
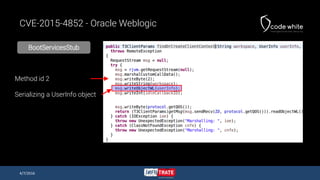
- 45. CVE-2015-4852 - Triggering the bug 4/7/2016 Stacktrace of the Weblogic Server while triggering the bug
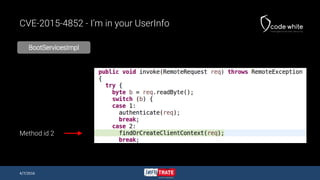
- 46. CVE-2015-4852 - I’m in your UserInfo BootServicesImpl 4/7/2016 Method id 2
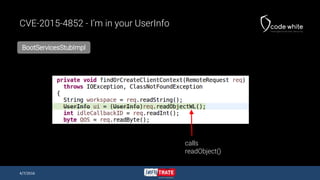
- 47. CVE-2015-4852 - I’m in your UserInfo BootServicesStubImpl 4/7/2016 calls readObject()
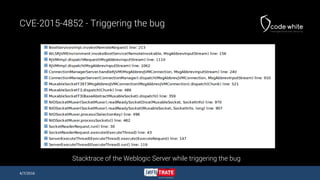
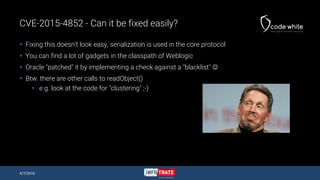
- 49. CVE-2015-4852 - Can it be fixed easily? Fixing this doesn’t look easy, serialization is used in the core protocol You can find a lot of gadgets in the classpath of Weblogic Oracle "patched" it by implementing a check against a "blacklist" Btw. there are other calls to readObject() e.g. look at the code for "clustering" ;-) 4/7/2016
- 50. Infiltrate gift= 0day Why always bashing Oracle There is more enterprise software out there! How about software from Germany? 4/7/2016
- 51. SAP Netweaver AS Java - 0day 4/7/2016
- 52. SAP Netweaver AS Intro SAP has two Application Servers SAP Netweaver AS ABAP SAP Netweaver AS JAVA SAP Netweaver AS JAVA is mainly used for Portal Process Integration (=ESB) Solution Manager BI (dual stacked system) There are many open ports, starting from 50000 4/7/2016
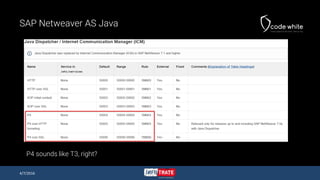
- 53. SAP Netweaver AS Java P4 sounds like T3, right? 4/7/2016
- 54. SAP Netweaver AS Java 4/7/2016
- 55. SAP Netweaver AS Java - How I found the bug It took more time to get a running version of Netweaver compared to finding the bug Used a VM from SAP Cloud Appliance Library hosted on AWS Same approach as with Oracle Weblogic Looking for a client program and searching for ObjectOutputStream.writeObject() Affects at least version 7.1, 7.2, 7.3 and 7.4 4/7/2016
- 56. SAP Netweaver AS Java - Exploiting the bug Netweaver runs its own SAP JRE Chris Frohoff’s universal JRE gadget works well Tested with Netweaver AS Java 7.3 and 7.4, should work with 7.1 / 7.2 4/7/2016
- 57. SAP Netweaver AS Java - POC 4/7/2016 REDACTED
- 58. SAP Netweaver AS Java 4/7/2016 DEMO
- 59. More to come? Sure! Bugs & Gadgets I already mentioned that Java Messaging is using Serialization heavily Currently I’m working on the Java Messaging Exploitation Tool (JMET) Integrates Chris Frohoff’s ysoserial Pwns your queues/topics like a boss! Planned to be released around summer ‘16 4/7/2016
- 60. Conclusion Java Deserialization is no rocket science Finding bugs is trivial, exploitation takes more So many products affected by it Research has started, again … This will never end! 4/7/2016
- 61. Q&A 4/7/2016
- 62. Java Deserialization Vulnerabilities – The forgotten bug class Matthias Kaiser


![Overview of Java’s Object Serialization Protocol
4/7/2016
Magic
class name
field type
class field
Class description info
TC_OBJECT
TC_CLASSDESC
classdata[]](https://image.slidesharecdn.com/javadeserializationvulnerabilitestheforgottenbugclassv1-160412140141/85/Java-Deserialization-Vulnerabilities-The-Forgotten-Bug-Class-8-320.jpg)


![Exploitation tricks
Adam Gowdiak’s TemplatesImpl
com.sun.org.apache.xalan.internal.xsltc.trax.TemplatesImpl is serializable
Allows to define new classes from your byte[ ][ ]
Calling TemplatesImpl.newTransformer() on deserialized object Code Execution
4/7/2016](https://image.slidesharecdn.com/javadeserializationvulnerabilitestheforgottenbugclassv1-160412140141/85/Java-Deserialization-Vulnerabilities-The-Forgotten-Bug-Class-31-320.jpg)